0x00 簡介
Cobalt Strike是一款常用于後滲透的神器,這個工具以團隊作為主體,共享資訊,擁有多種協定上線方式,內建了端口轉發,端口掃描,socket代理,提權,釣魚等。除去自身功能外,Cobalt Strike還利用了Metasploit和Mimikatz等其他知名工具的功能。
0x01 Cobalt Strike 架構
檔案結構
│ agscript 拓展應用的腳本
│ c2lint 檢查profile的錯誤異常
│ cobaltstrike
│ cobaltstrike.jar 用戶端程式
│ icon.jpg
│ license.pdf
│ readme.txt
│ releasenotes.txt
│ teamserver 服務端程式
│ update
│ update.jar
│
└─third-party 第三方工具
README.vncdll.txt
vncdll.x64.dll
vncdll.x86.dll 複制
個人定制
- Cobalt Strike可以使用 AggressorScripts腳本來加強自身,能夠擴充菜單欄,Beacon指令行,提權腳本等
- Cobalt Strike通信配置檔案是 Malleable C2 你可以修改 CS的通訊特征,Beacon payload的一些行為
- Cobalt Strike可以引用其他的通訊架構ExternalC2,ExternalC2是由Cobalt Strike提出的一套規範/架構,它允許黑客根據需要對架構提供的預設HTTP(S)/DNS/SMB C2 通信通道進行擴充。
總的來說 CS的自定義功能很強大,使用起來很靈活後期,會講到相關的使用。
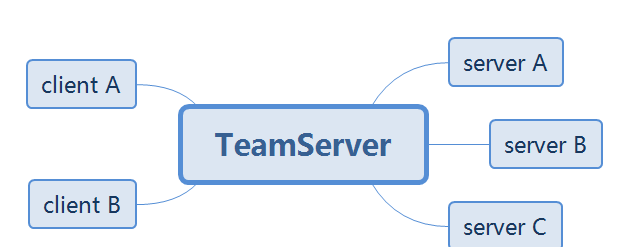
0x02 運作
Cobalt Strike 需要團隊伺服器才能使用,也就是teamserver。 需要檔案 teamserver 與 cobaltstrike.jar 可以選擇把他放在公網上面
啟動團隊伺服器
執行 sudo ./teamserver 複制
./teamserver <host> <password> [/path/to/c2.profile] [YYYY-MM-DD]
<host> is the (default) IP address of this Cobalt Strike team server
<password> is the shared password to connect to this server
[/path/to/c2.profile] is your Malleable C2 profile
[YYYY-MM-DD] is a kill date for Beacon payloads run from this server 複制
在沒有使用 自己的Malleable C2 profile情況下隻填host 與 password即可
啟動CS ./cobaltstrike.jar
其中user就是你想要輸入的名字,password 為啟動teamserver的密碼
進入主檔案
0x03 菜單欄功能
Cobalt Strike
New Connection //新的連結
Preferences 偏好設定
Visualization 視窗視圖模式
V** interfaces V**接入
Listeners 監聽器
Sript Manager 腳本管理
Close 退出 複制
其中 Preferences 可以删除 登陸記錄的賬戶密碼 與team server SSL ,其他的就是軟體的一些顔色等。
View
Applications 用于顯示 System Profiler 擷取的目标浏覽器,作業系統,flash版本
Credentials 顯示所有已經擷取的使用者主機hash
Downloads 顯示下載下傳的檔案
Event log 事件日志 記錄團隊 目标上線等記錄
Keystrokes 目标鍵盤記錄
Proxy Pivots 代理資訊
Screenshots 螢幕截圖
Script Console 加載自定義腳本
Targets 顯示所有主機
Web log web服務日志 複制
Attack
Packages
HTML Application 生成hta檔案
MS Office Macro 宏office檔案
Payload Generator 生成各種語言版本的payload
USB/CD AutoPlay 利用自動播放運作的被控端檔案
Windows Dropper 捆綁器可将任意正常的檔案
Windows Executable payload生成可執行檔案 (一般使用這個)
Windows Executable (S) 把包含payload,Stageless生成可執行檔案(包含多數功能) 複制
Web Drive-by
Manage 開啟的所有web服務
Clone Site 克隆網站
Host File 提供Web以供下載下傳某檔案
Scripted Web Delivery 為payload提供web服務以便于下載下傳和執行
Signed Applet Attack 啟動一個Web服務以提供自簽名Java Applet的運作環境
Smart Applet Attack 自動檢測Java版本并l利用已知的exploits繞過security
System Profiler 擷取系統,Flash,浏覽器版本等 複制
Spear Phish 魚叉式網絡釣魚 複制
Reporting
Activity report 活動報告
Hosts report 主機報告
Indicators of Compromise 威脅報告
Sessions report 會話報告
Social engineering report 社會工程學報告 複制
0x04 右鍵功能
Interact 打開beacon
Access
dump hashes 擷取hash
Elevate 提權
Golden Ticket 生成黃金票據注入目前會話
MAke token 憑證轉換
Run Mimikatz 運作 Mimikatz
Spawn As 用其他使用者生成Cobalt Strike偵聽器
Explore
Browser Pivot 劫持目标浏覽器程序
Desktop(VNC) 桌面互動
File Browser 檔案浏覽器
Net View 指令Net View
Port scan 端口掃描
Process list 程序清單
Screenshot 截圖
Pivoting
SOCKS Server 代理服務
Listener 反向端口轉發
Deploy V** 部署V**
Spawn 新的通訊模式并生成會話
Session 會話管理,删除,心跳時間,退出,備注 複制
Beacon
beacon> help
Beacon Commands
===============
Command Description
------- -----------
browserpivot Setup a browser pivot session
bypassuac Spawn a session in a high integrity process
cancel Cancel a download that's in-progress
cd Change directory
checkin Call home and post data
clear Clear beacon queue
covertV** Deploy Covert V** client
cp Copy a file
dcsync Extract a password hash from a DC
desktop View and interact with target's desktop
dllinject Inject a Reflective DLL into a process
download Download a file
downloads Lists file downloads in progress
drives List drives on target
elevate Try to elevate privileges
execute Execute a program on target
exit Terminate the beacon session
getsystem Attempt to get SYSTEM
getuid Get User ID
hashdump Dump password hashes
help Help menu
inject Spawn a session in a specific process
jobkill Kill a long-running post-exploitation task
jobs List long-running post-exploitation tasks
kerberos_ccache_use Apply kerberos ticket from cache to this session
kerberos_ticket_purge Purge kerberos tickets from this session
kerberos_ticket_use Apply kerberos ticket to this session
keylogger Inject a keystroke logger into a process
kill Kill a process
link Connect to a Beacon peer over SMB
logonpasswords Dump credentials and hashes with mimikatz
ls List files
make_token Create a token to pass credentials
mimikatz Runs a mimikatz command
mkdir Make a directory
mode dns Use DNS A as data channel (DNS beacon only)
mode dns-txt Use DNS TXT as data channel (DNS beacon only)
mode dns6 Use DNS AAAA as data channel (DNS beacon only)
mode http Use HTTP as data channel
mode smb Use SMB peer-to-peer communication
mv Move a file
net Network and host enumeration tool
note Assign a note to this Beacon
portscan Scan a network for open services
powerpick Execute a command via Unmanaged PowerShell
powershell Execute a command via powershell.exe
powershell-import Import a powershell script
ppid Set parent PID for spawned post-ex jobs
ps Show process list
psexec Use a service to spawn a session on a host
psexec_psh Use PowerShell to spawn a session on a host
psinject Execute PowerShell command in specific process
pth Pass-the-hash using Mimikatz
pwd Print current directory
rev2self Revert to original token
rm Remove a file or folder
rportfwd Setup a reverse port forward
runas Execute a program as another user
runu Execute a program under another PID
screenshot Take a screenshot
shell Execute a command via cmd.exe
shinject Inject shellcode into a process
shspawn Spawn process and inject shellcode into it
sleep Set beacon sleep time
socks Start SOCKS4a server to relay traffic
socks stop Stop SOCKS4a server
spawn Spawn a session
spawnas Spawn a session as another user
spawnto Set executable to spawn processes into
spawnu Spawn a session under another PID
ssh Use SSH to spawn an SSH session on a host
ssh-key Use SSH to spawn an SSH session on a host
steal_token Steal access token from a process
timestomp Apply timestamps from one file to another
unlink Disconnect from parent Beacon
upload Upload a file
wdigest Dump plaintext credentials with mimikatz
winrm Use WinRM to spawn a session on a host
wmi Use WMI to spawn a session on a host 複制
此部分不做翻譯 講在後期使用中介紹 也可在Beacon 使用
help xxxx
擷取更加詳細的介紹 (翻譯太累了=.=)
0x06文末
本文介紹Cobalt Strike3.8版本的運作以及大體功能的翻譯,後期功能示範可能會換成其他版本。
來源:Ms08067安全實驗室